Introduction: The Invisible Battlefield
Fifth-generation fighters are no longer just about thrust, stealth, and kinematics. They are
networked computing nodes operating inside a contested electromagnetic spectrum.
The F-35 Lightning II and the Sukhoi Su-57 “Felon” represent two very different philosophies of
cyber resilience, network defense, and fleet integration.
Understanding the true cost of cyber resilience means looking beyond radar cross-section numbers and missile loadouts, and
examining the software architectures, data links, and logistics clouds that keep these aircraft combat-ready.
The F-35’s Digital Nervous System: From ALIS to ODIN
The F-35 was designed from day one as a system-of-systems. Its mission computers, sensors, logistics, and maintenance are
tightly coupled with an external digital backbone. Originally, this role was fulfilled by the
Autonomic Logistics Information System (ALIS), which faced criticism for complexity.
In response, the program migrated to ODIN (Operational Data Integrated Network). Key design goals include:
- Zero-trust principles: Every user, device, and data flow must be authenticated.
- Stronger encryption and hardened communication channels.
- Containerized services for easier isolation, patching, and scaling.
- Predictive analytics for proactive maintenance.
This gives the F-35 ecosystem a powerful cyber toolkit, but at a price: constant software updates, specialized personnel, and
secure data centers. Cyber resilience for the F-35 is a permanent operational cost.
Su-57’s Cyber Philosophy: Isolation over Hyper-Integration
The Su-57 follows a more localized and less cloud-dependent approach. Its avionics suite integrates radar, infrared
search and track (IRST), and navigation, but external digital dependencies are strictly limited.
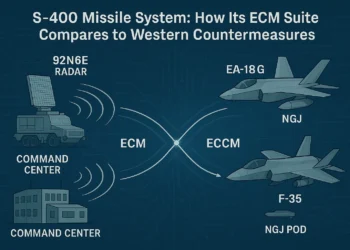
The Su-57 leverages its powerful built-in L-402 Tarak electronic warfare (EW) suite, which integrates radar jamming and
electronic counter-countermeasure (ECCM) functions directly into the aircraft’s skin. Russian designers emphasize compartmentalization:
- Mission-critical subsystems are designed to remain functional with minimal external connectivity.
- Data exchange relies on line-of-sight encrypted datalinks rather than global cloud platforms.
This philosophy reduces the remote attack surface but limits the depth of multi-domain data fusion compared to the F-35.
The Philosophical Divide: F-35 vs. Su-57 Cyber Resilience
| Metric | F-35 (ODIN) 🇺🇸 | Su-57 (Localized) 🇷🇺 |
|---|---|---|
| Core Philosophy | Hyper-Integration | Compartmentalization |
| Logistical Dependency | High – ODIN / Global Cloud | Low – Line-of-sight Datalinks |
| Cyber Vulnerability | Broader external attack surface | Reduced surface, less fusion |
| Cost Profile | High recurring software costs | High hardware integration costs |
Integration vs. Digital Sovereignty
The F-35 model is built around deep integration. Allied fleets share common software baselines and mission data.
This creates high interoperability but raises questions of digital sovereignty. Users rely on an external ecosystem for updates,
and access can be constrained by alliance politics.
The Su-57 model priorities national control. Software and encryption are largely kept inside Russia’s own infrastructure.
This offers sovereignty but sacrifices the “network effects” of a global fleet.
Weakness Analysis: Cyber Trade-Offs
| Aspect | F-35 (ODIN Model) | Su-57 (Localized Model) |
|---|---|---|
| Attack Surface | Broad (Global Connectivity) | Narrow (Air-gapped logic) |
| Update Velocity | High (Continuous Patching) | Low (Scheduled Upgrades) |
| Interoperability | Very High (NATO Standard) | Low (National Standard) |
| Long-Term Flexibility | Strong (Software Defined) | Rigid (Hardware Dependent) |
FAQ: Cyber Resilience in 5th-Gen Fighters
Is the F-35 more vulnerable because it is connected?
Greater connectivity creates more theoretical entry points. However, it also enables faster patching and centralized defense (ODIN), similar to how a modern smartphone is updated frequently against threats.
Does the Su-57’s isolation make it “safer”?
Isolation reduces remote hacking risks (“Air Gap” security). However, it makes the aircraft slower to adapt to new electronic threats compared to the F-35’s rapid software updates.
How much does cyber resilience cost?
For the F-35, it adds billions in lifecycle software management. For the Su-57, the cost is front-loaded into expensive onboard EW hardware (like the L-402 suite) rather than cloud infrastructure.
Conclusion: Code as the New Armor
In modern air combat, code is a form of armor. The F-35’s model delivers unparalleled situational awareness at the expense of complexity. The Su-57’s sovereign architecture reduces exposure but risks falling behind in the data-driven evolution of tactics.
The true cost of cyber resilience is not measured only in dollars, but in how effectively an air force balances security, sovereignty, and speed of adaptation.